Using AWS Toolkit for Visual Studio
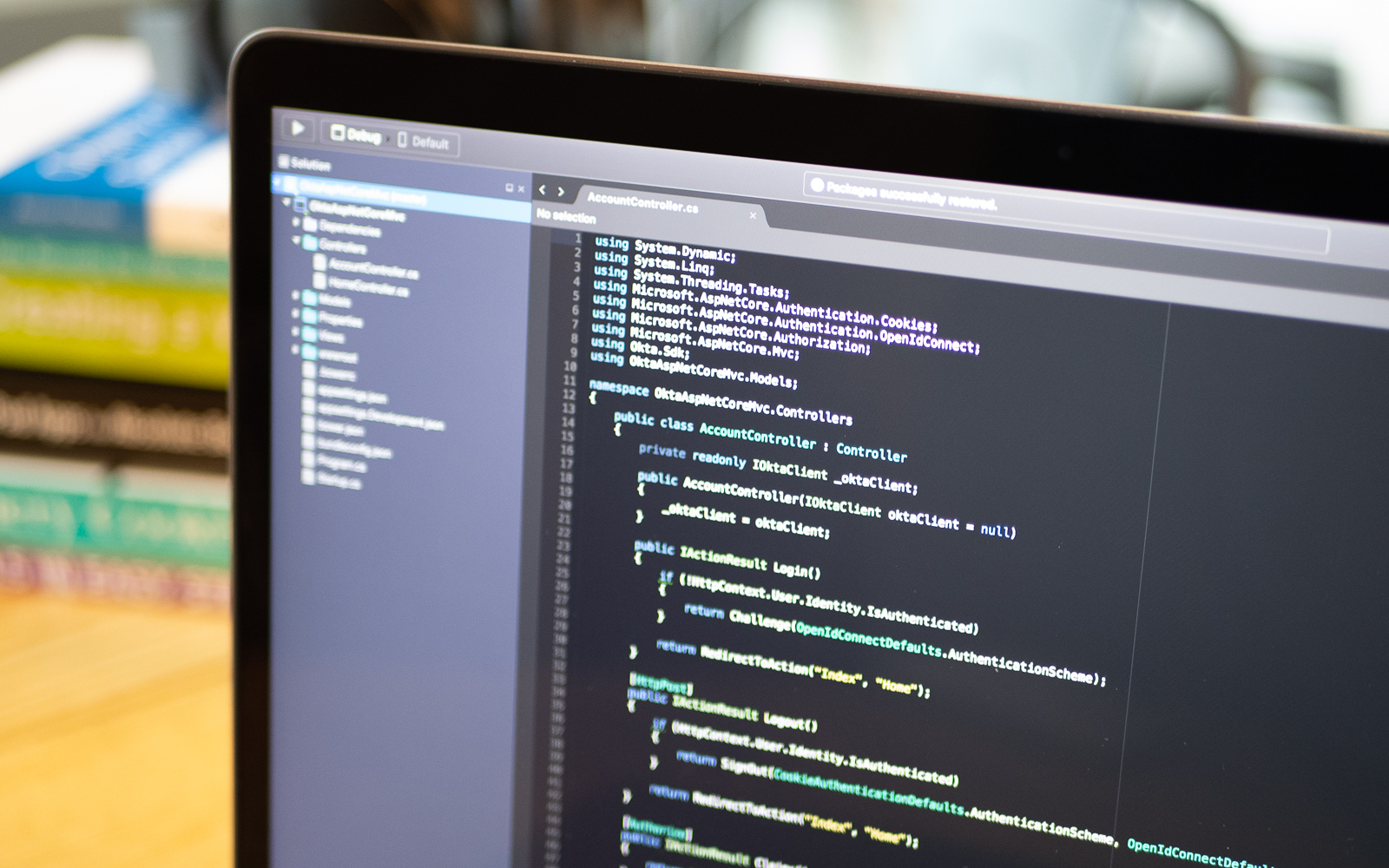
Amazon Web Services is one of the most popular cloud computing platforms on the planet. There’s a good chance you will need to work in an AWS environment, which means publishing to one of their web server services like Elastic Beanstalk. The AWS platform is enormous, and this can be an intimidating task for a developer. Luckily, Amazon has released their AWS Toolkit for Visual Studio 2013-2015 and AWS Toolkit for Visual Studio 2017-2019, which...
Web Forms Migration to Blazor in .NET Core
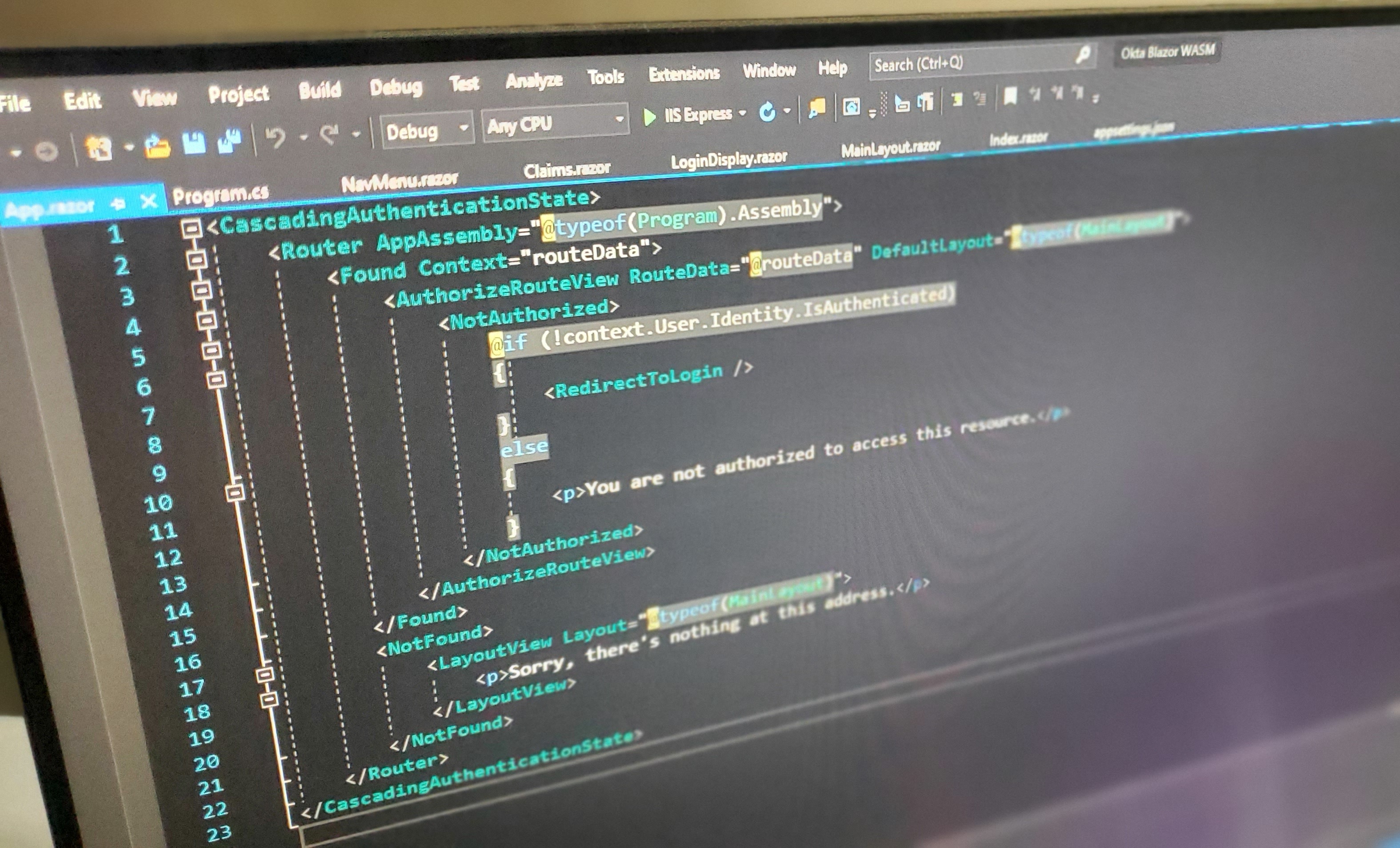
ASP.NET Web Forms framework has been the cornerstone technology of .Net for web development since the release of .Net Framework in 2002. ASP.NET Web Forms includes a layer of abstraction for developers so that you don’t need to care about HTML, JavaScript, or any other front-end technology. It provides a development flow similar to building desktop apps, a way for developers to build a web page by drag and drop, an event-driven programming model, and...
Getting Started with Libsodium in Python and Go
The Networking and Cryptography library (NaCl pronounced “salt”) is a software library that provides the core operations required to build cryptographic tools. Sodium is a fork of NaCl with an extended API; it’s portable, and binaries are available to be used by various programming languages and operating systems. It comes in the form of a library called libsodium. Although there are several Python and Go cryptography libraries, it is primarily a matter of personal choice...
Content Negotiation with a Java MicroProfile Application

Content negotiation allows for an HTTP server to respond to different types of clients. Many modern clients expect a JSON response, but there may be a need to format responses differently, maybe XML for older clients or a binary format for newer ones. Content negotiation is the mechanism used to solve that problem and others, such as dealing with multiple languages and even compressing HTTP requests. In this post, I’ll walk through building a simple...
Fixing Common Problems with CORS and JavaScript
Many websites have JavaScript functions that make network requests to a server, such as a REST API. The web pages and APIs are often in different domains. This introduces security issues in that any website can request data from an API. Cross-Origin Resource Sharing (CORS) provides a solution to these issues. It became a W3C recommendation in 2014. It makes it the responsibility of the web browser to prevent unauthorized access to APIs. All modern...
Spring WebClient for Easy Access to OAuth 2.0 Protected Resources

Spring ẀebClient was added as part of the reactive web stack WebFlux in Spring Framework 5.0. WebClient allows performing HTTP requests in reactive applications, providing a functional and fluent API based on Reactor, and enabling a declarative composition of asynchronous non-blocking requests without the need to deal with concurrency. One of its features is support for filter registration, allowing to intercept and modify requests, which can be used for cross-cutting concerns such as authentication, as...
How to Toggle Functionality in C# with Feature Flags
Toggling functionality using feature flags in .NET Core apps is quite straightforward, especially with a neat little feature flag management service. In this post, I’ll walk you through how to build a simple web application using Okta for user authentication and how to use ConfigCat to manage and access feature flags. What Are Feature Flags? Feature flags (aka. feature toggles) are a relatively new software development technique that enables development teams to turn features on...
Easy Distributed Tracing with Spring Cloud Sleuth

Spring Cloud Sleuth allows you to aggregate and track log entries as requests move through a distributed software system. In a monolithic system, it’s relatively easy to track requests as they move through the codebase because all requests can easily be logged to the same log file. You can generally just filter the log by the thread ID. But in a distributed system, a single client request may sprawl across any number of discrete cloud...
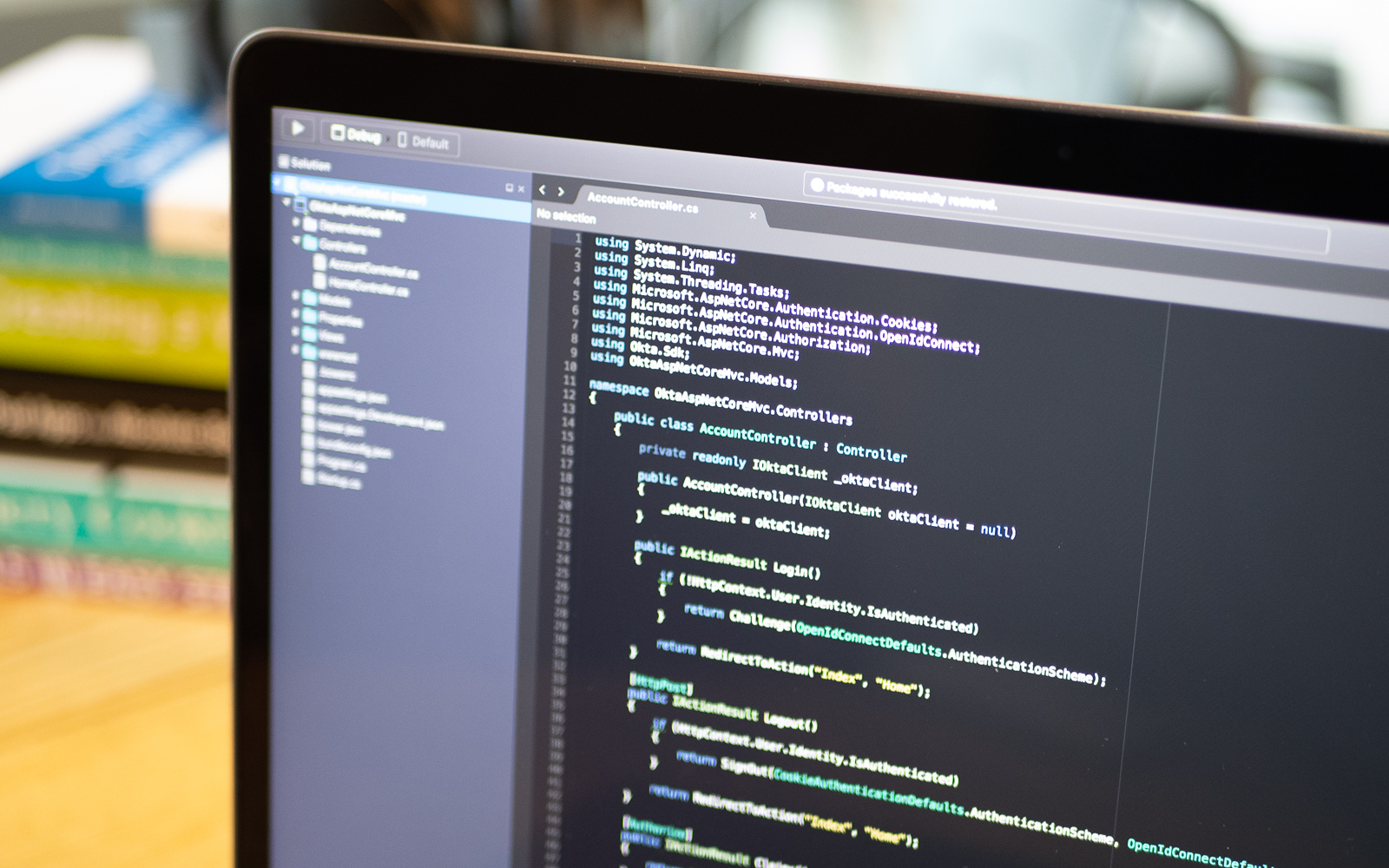
How to Write a Secure Python Serverless App on AWS Lambda
Modern authentication systems generate JSON Web Tokens (JWT). While there are several types of JWTs, we’re concentrating on access tokens. When a user successfully logs in to an application, a JWT is generated. The token is then passed in all requests to the backend. The backend can then validate the token and reject all requests with invalid or missing tokens. Today, we are going to build a simple web application that uses the Okta authentication...
Easy Xamarin Forms Auth with PKCE

OAuth 2.0 is a protocol that controls authorization to access a secured resource such as a native app, web app, or API server. For native applications, the recommended method for controlling access between your application and a resource server is the Authorization Code flow with a Proof Key for Code Exchange (PKCE). In this article, you will learn how to build a basic cross-platform application with Xamarin.Forms and implement Authorization Code flow with PKCE using...