Set Access Control Policies With Kong Konnect and Okta

In our last Kong and Okta tutorial, we will implement a basic access control policy based on Okta’s groups and planes. This series will show you how to implement service authentication and authorization for Kong Konnect and Okta using the OpenID Connect (OIDC) plugin. Parts 1, 2 and 3 covered:
- Implement client credentials for application authentication
- Authorization Code for user authentication
- Implement introspection flow for token validation
Table of Contents
- How Access Control Works
- Configure Okta
- Enable OpenID Connect Plugin
- Consume the Kong Route
- Protect Your Applications With Kong Konnect and Okta
You can also watch this tutorial as a screencast.
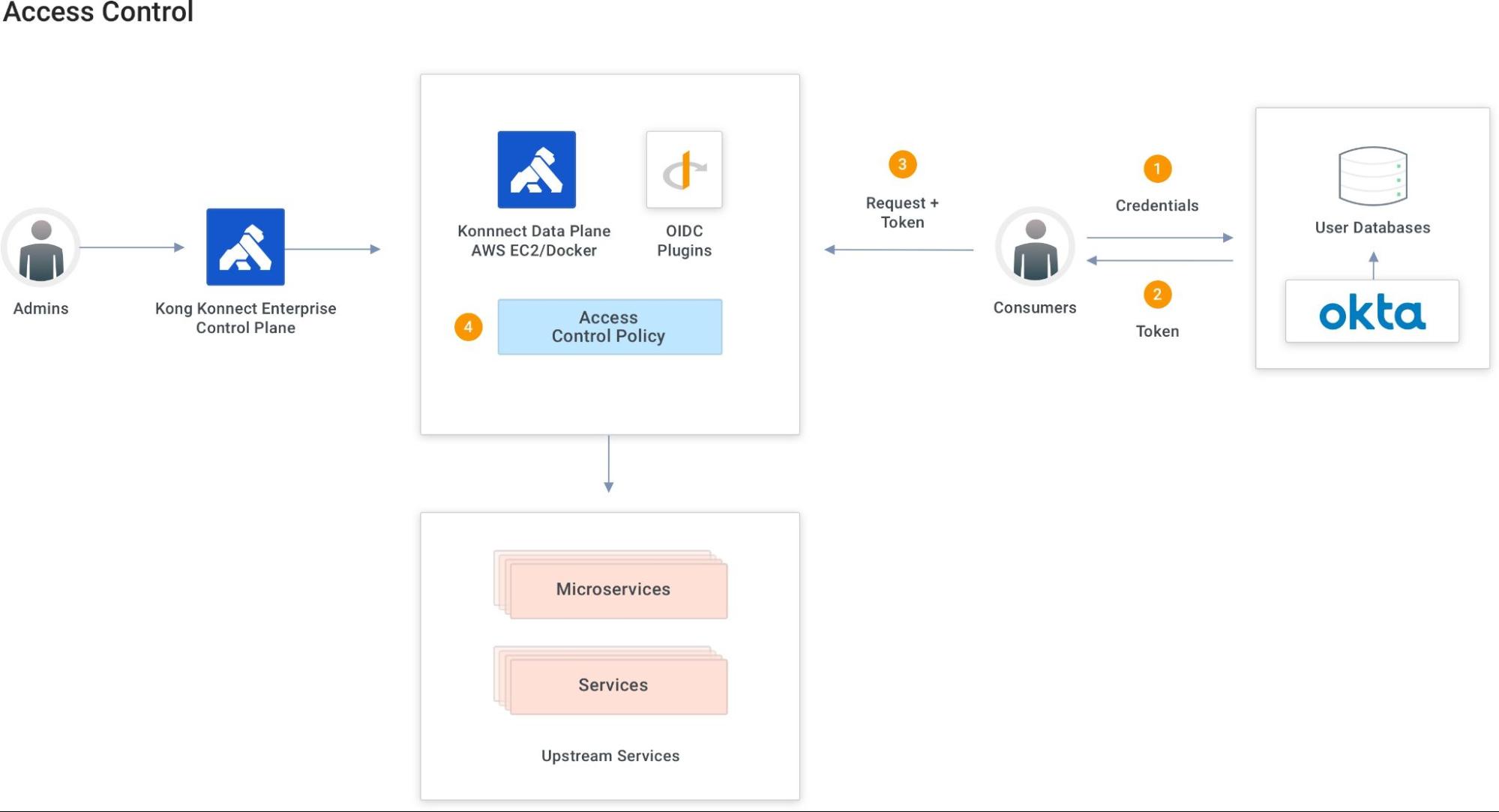
How Access Control Works
OIDC claims are a piece of information inserted about an entity. Name and picture are claim examples for users.
OIDC scopes are a group of claims.
In this tutorial, we’ll define a new claim based on an Okta group. The claim will be included in all scopes defined. The OIDC plugin must check if the coming tokens have this specific claim to allow the Kong route consumption. Only users who are part of the Okta group will have the claim included in the token and will be able to consume the route.
Configure Okta
In my example, I already created two users and a group. The group has only one member.
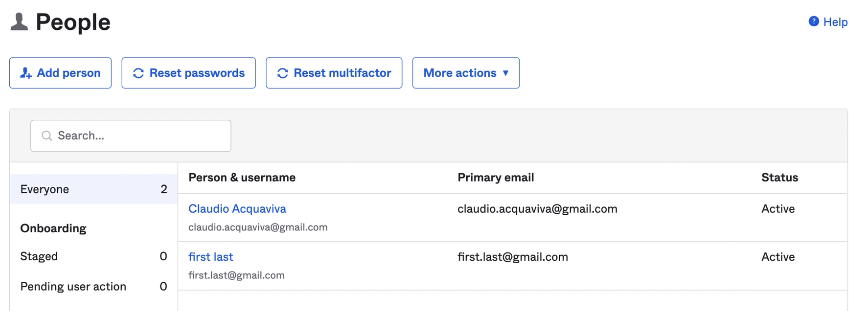
The new claim will be based on this group, so only its members will have permission to go through the Kong route.
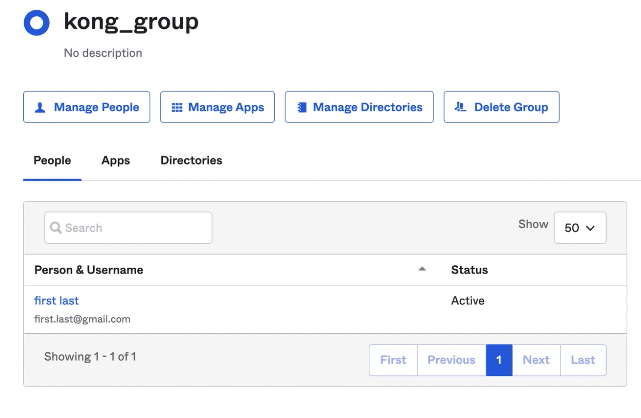
The new Kong claim definition is based on the Kong group. It’ll be included in any scope for each access token issued.
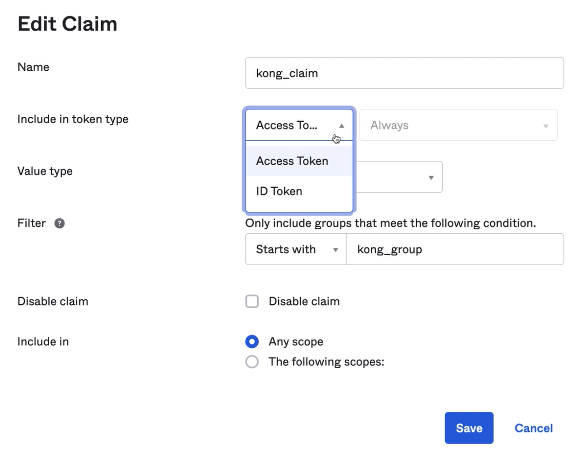
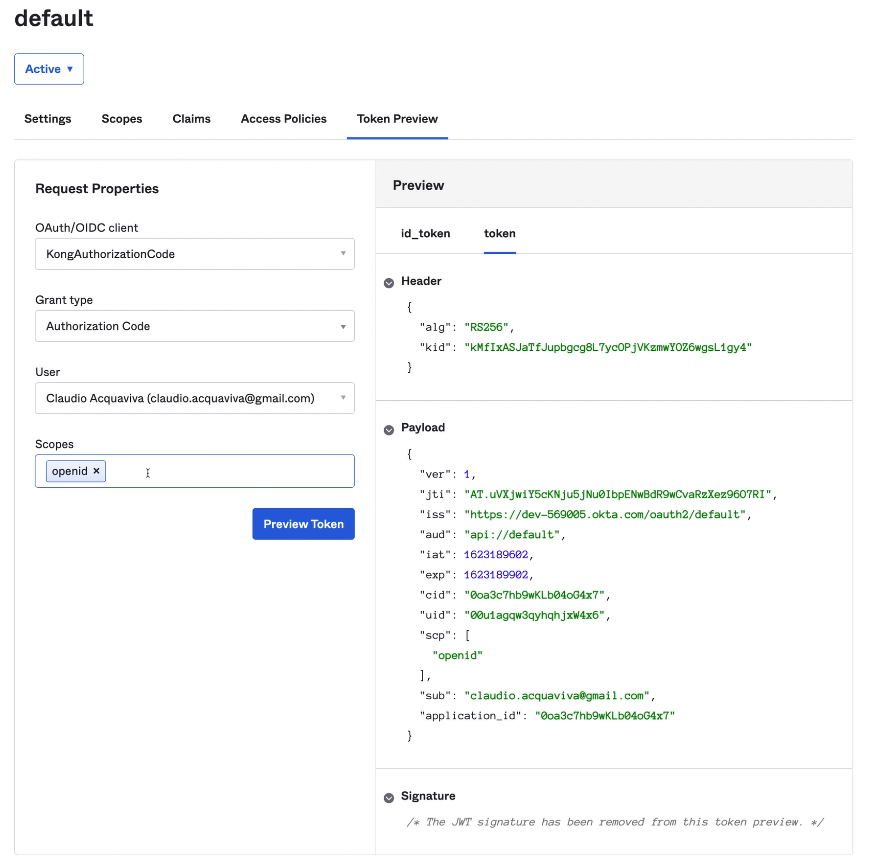
Let’s run a token preview to check the tokens and claim out. For the first request, we can try the user who’s not a Kong group member. As expected, the access token does not have a Kong claim inside of it.
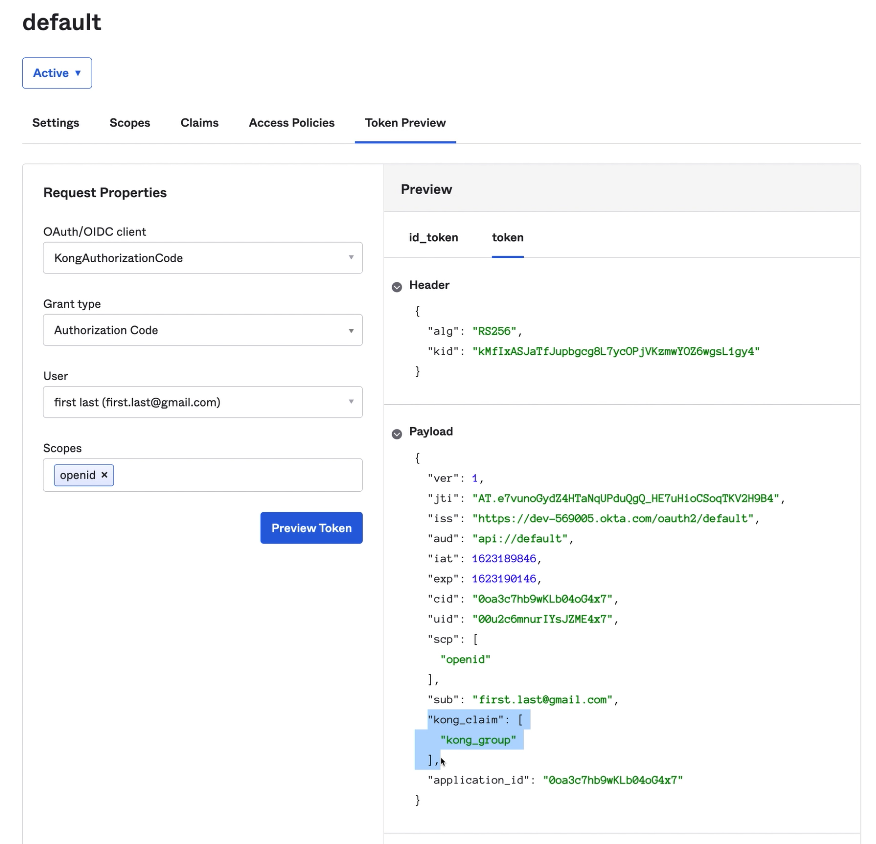
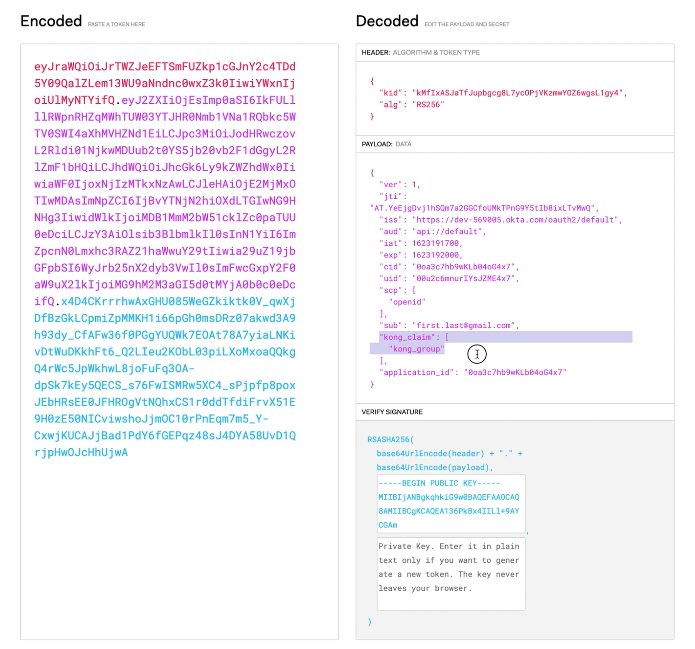
If we try the other user that belongs to the Kong group, the access token will be different. Here’s the Kong claim inside our token.
Enable OpenID Connect Plugin
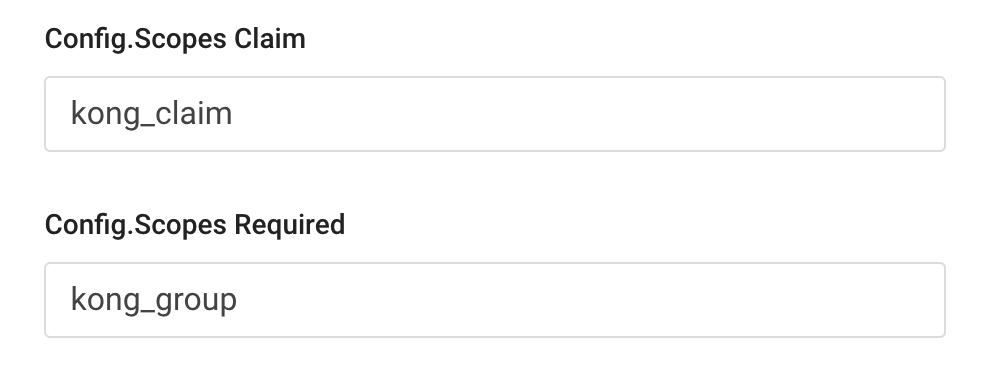
Let’s check our Kong route with the OIDC plugin enabled. According to the parameters in the screenshot below, the plugin should check if the token has the Kong claim defined by Okta. So in this sense, the route should be consumed only by users who are members of the Kong group.
- Config.Scope Claim:
kong_claim - Config.Scopes Required:
kong_group
Consume the Kong Route
Let’s have both users consume the route. The process will be similar to what we already did in Okta’s token preview process. For the first request, let’s try the user who isn’t in the Kong group. As expected, we shouldn’t be able to consume the route.
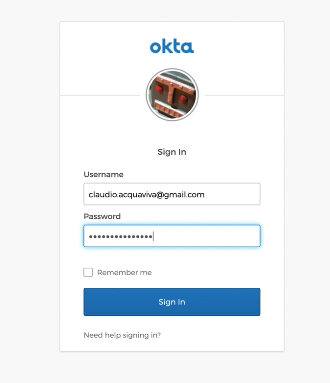
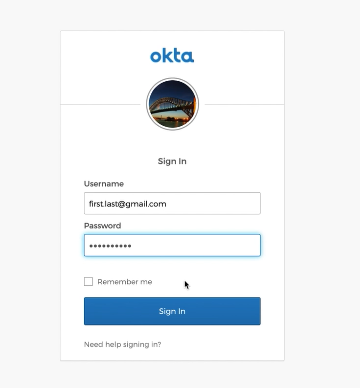
We are trying to consume the route, but since we don’t have any token injected inside our request, the API gateway redirects us to Okta to present our credentials.
And after getting authenticated, Okta is redirecting us back to the API gateway. However, since the token doesn’t have the claim inside it, the gateway says “forbidden” and won’t allow us to consume the route.
Let’s try the other user who is a member of the Kong group. Again, we try to consume the route, getting redirected to Okta, but we’re going to use the second user this time.
After getting authenticated, Okta redirects us back to the API gateway. This time, our token has the Kong claim we defined in Okta previously.
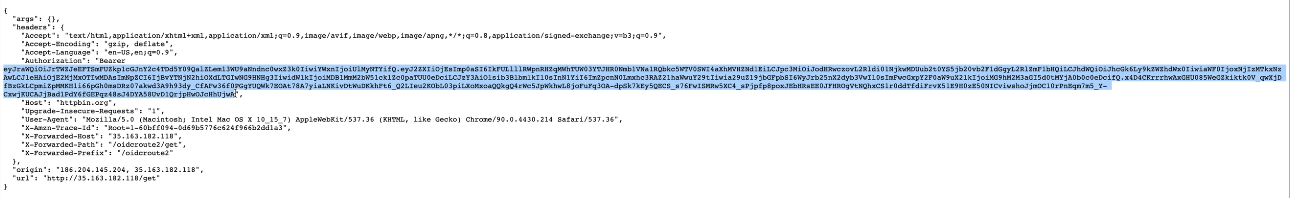
If we go to jwt.io, we will decode the JWT token and check the token and the claim inside it.
Protect Your Applications With Kong Konnect and Okta
Start a free trial, or contact Kong if you have any questions as you’re getting set up.
Once you’ve set up Konnect and Okta access control policies, you may find these other tutorials helpful:
- Automating Your Developer Pipeline With APIOps (DevOps + GitOps)
- Service Design Guidelines Part 2: API Versioning
- “Gateway Mode” in Kuma and Kong Mesh
- Use Kong Gateway to Centralize Authentication
If you have any questions, please leave a comment below. To be notified when the OktaDev team posts new content, please follow @oktadev on Twitter, like them on LinkedIn, or subscribe to their YouTube channel.
Okta Developer Blog Comment Policy
We welcome relevant and respectful comments. Off-topic comments may be removed.